Even space systems in the far reaches of orbit are susceptible to cyber attacks. Once on orbit and equipped with computer hardware and software that cannot be easily updated, these systems risk becoming easy targets for these attacks. Even worse, engineers on the ground have little way of knowing that their system has been compromised.
The Watcher, an ongoing project of researchers at Aerospace, aims to toughen the cyber defenses of national security spacecraft, including those already on orbit. The cyber threat evolves at a much faster rate than spacecraft are designed and deployed. A system was needed to offer additional cyber protection after a spacecraft is launched.
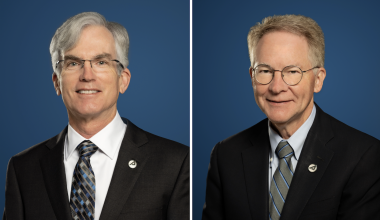
As explained by Kenneth Lau, Systems Director, Systems Engineering and Development, an effective cyber strategy involves five essential steps: deter, detect, identify, destroy, and recover. The Watcher focuses on the second item—detecting cyber intrusions.
Once the program is equipped, The Watcher works as an onboard monitoring function that can detect suspicious activity on a satellite. At the program's core is an artificial intelligence engine that learns the normal states of a spacecraft and identifies even slight deviations.
The Watcher can detect malicious commands, malware, and software implants inserted after a spacecraft's launch and can intervene before they are executed by operating inside the flight software control loop, ensuring survivability.
Lau and his team developed processes and techniques to discriminate cyber intrusions from normal anomalies. The next step was to package them in a portable, standalone format that could be sent to an operational spacecraft.
"The time frame of how to protect the current flying fleet, as well as near-term launches, is what led to the development of The Watcher," Lau said. "It is a pure software-based protection and can be uploaded to a space vehicle on orbit or near launch with minimal degradation in performance and schedule."
The system is very nonintrusive. Flight software is not directly affected, nor is the space vehicle operating system. "It is neither part of the operating system nor the application," he said. "It is standalone and can monitor both the operating system and application."
Moreover, he said, the technology can be tailored for any space vehicle and is not limited to space vehicle computers; payload computers can be protected as well. The Watcher is agnostic to the type and origin of cyber intrusions, effectively weeding out malicious commands inserted through the communications uplink or onboard implants or from external spacecraft.
At its core [The Watcher] is an artificial intelligence engine that learns the normal states of a spacecraft and identifies even slight deviations.
One feature of The Watcher is that it is able to speed up or slow down the space vehicle software in order to make it easier to detect hacking attempts. Such research has also helped Aerospace identify other space vehicle vulnerabilities and mitigation techniques.
The Watcher was recently flown on ANGELS (Automated Navigation and Guidance Experiment for Local Space) to demonstrate its detection and data-capture capabilities in a realistic scenario. Developers continue to refine the technology. For example, future versions may include different algorithms optimized for either optical or radio frequency communications.
The research is part of a broader effort to combat the never-ending threat of cyberattack. "In the future, we envision an integrated hardware and software solution, where some sort of trusted hardware onboard a space vehicle, along with cyber-protection software, would help the space vehicle be more resistant to cyber intrusion," Lau said.
In the meantime, The Watcher provides a reliable defense that can be implemented relatively quickly. "It is easily uploaded to any on-orbit or near-launch space vehicle without significantly affecting schedule or existing capabilities," Lau said. "It allows the space vehicle to perform its primary mission while fighting cyber intrusions in the background."